SSH remote access is a powerful tool that enables users to securely connect and manage IoT devices, such as Raspberry Pi, from anywhere in the world. This technology has revolutionized how we interact with remote systems, making it easier to deploy, monitor, and maintain IoT projects. Whether you're a hobbyist or a professional developer, understanding SSH remote IoT Raspberry Pi and its free download options can significantly enhance your capabilities in managing remote devices.
As the Internet of Things (IoT) continues to expand, the demand for secure and efficient remote management solutions has increased. Raspberry Pi, a versatile and affordable single-board computer, has become a popular choice for IoT enthusiasts and professionals alike. By leveraging SSH (Secure Shell), users can remotely control their Raspberry Pi devices without compromising security.
In this article, we will explore the fundamentals of SSH remote IoT Raspberry Pi, including how to set it up, best practices for secure connections, and where to find free download options. Whether you're a beginner or an experienced developer, this guide will provide you with the knowledge and tools necessary to harness the full potential of SSH remote access for your IoT projects.
Read also:How Did George Die In Greys Anatomy Unraveling The Tragic Story
Table of Contents
- Introduction to SSH
- Raspberry Pi SSH Setup
- Benefits of SSH Remote IoT
- Securing Your SSH Connection
- Free SSH Clients for Raspberry Pi
- IoT Security Best Practices
- Troubleshooting SSH Connections
- SSH Alternatives for IoT
- Real-World IoT SSH Applications
- Conclusion and Next Steps
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over an unsecured network. It is widely used for remote command-line login and execution, enabling users to manage systems and applications remotely. SSH remote IoT Raspberry Pi has become a staple for developers working on IoT projects due to its reliability and security features.
SSH operates on port 22 by default and uses encryption to protect data transmitted between the client and server. This ensures that sensitive information, such as passwords and commands, remains confidential and tamper-proof. For Raspberry Pi users, SSH offers a convenient way to manage their devices without the need for a physical display or keyboard.
Why Use SSH for IoT?
- Secure communication between devices
- Remote access from anywhere in the world
- Compatibility with various operating systems
- Easy integration with IoT platforms
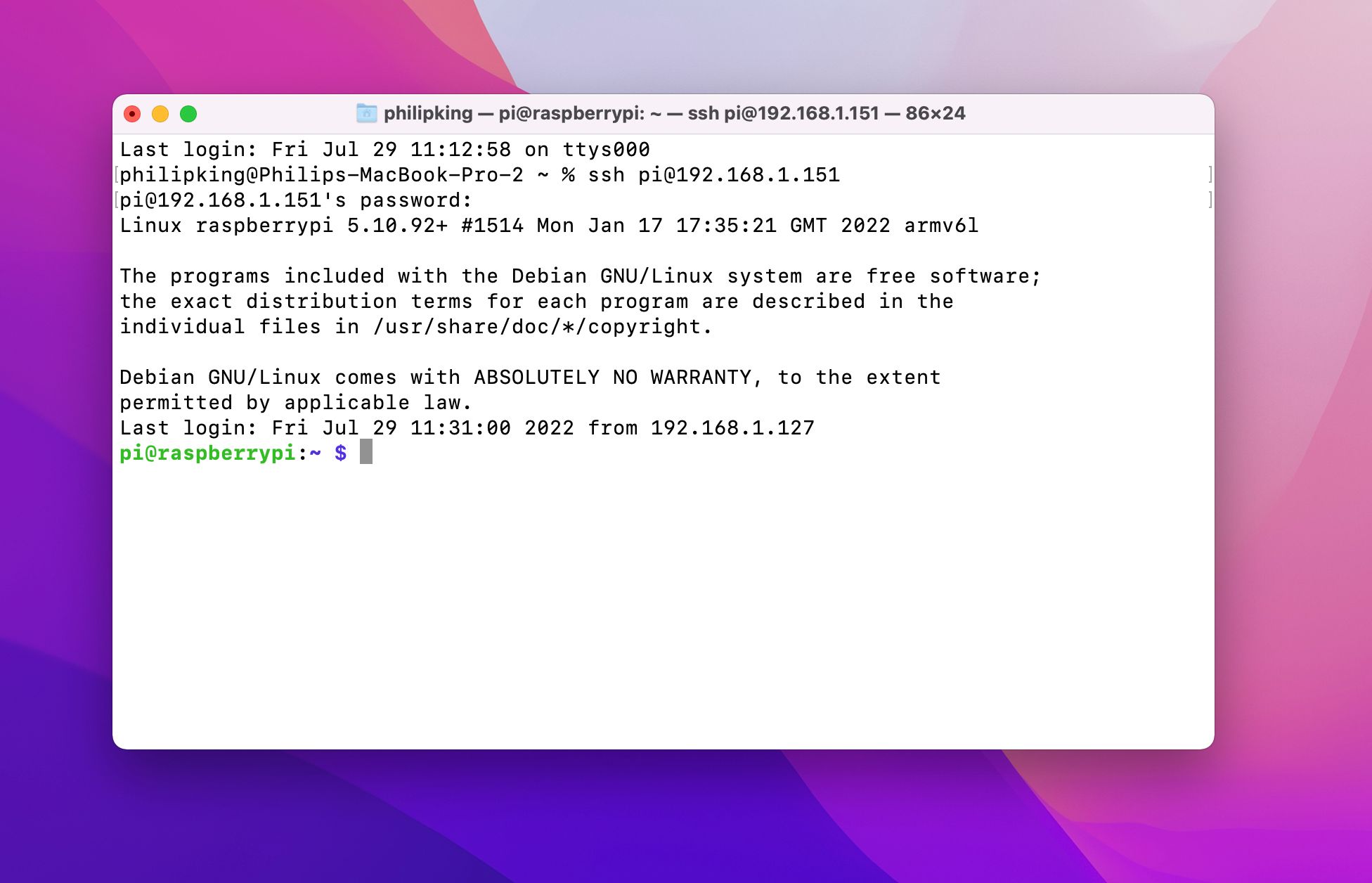
Raspberry Pi SSH Setup
Setting up SSH on a Raspberry Pi is a straightforward process. By default, SSH is disabled on the latest versions of Raspberry Pi OS, but it can be easily enabled through the desktop interface or by modifying configuration files.
Enabling SSH via Desktop
- Open the Raspberry Pi Configuration tool from the Preferences menu.
- Select the Interfaces tab.
- Set SSH to Enabled and click OK.
Enabling SSH via Command Line
If you're using a headless setup (no monitor or keyboard), you can enable SSH by adding an empty file named "ssh" to the boot partition of your Raspberry Pi SD card. Here's how:
- Insert the SD card into your computer.
- Open the boot partition and create a new file named "ssh" (no extension).
- Eject the SD card and insert it into your Raspberry Pi.
Benefits of SSH Remote IoT
Using SSH for IoT projects offers numerous advantages, making it a preferred choice for remote device management. Below are some of the key benefits:
- Security: SSH encrypts all data transmitted between the client and server, ensuring confidentiality and integrity.
- Convenience: With SSH, you can manage your IoT devices from anywhere, as long as you have an internet connection.
- Flexibility: SSH supports a wide range of commands and tools, allowing you to perform complex tasks remotely.
- Cost-Effective: Since SSH is a built-in feature of many operating systems, there are no additional costs associated with its use.
Securing Your SSH Connection
While SSH is inherently secure, there are additional steps you can take to further protect your IoT devices from unauthorized access:
Read also:American Spirit Blues The Journey Of A Timeless Sound
Use Strong Passwords
Ensure that all user accounts on your Raspberry Pi have strong, complex passwords. Avoid using default credentials, as these are often targeted by hackers.
Enable Public Key Authentication
Public key authentication is a more secure alternative to password-based authentication. By generating a public-private key pair, you can eliminate the need for passwords entirely.
Change the Default SSH Port
Changing the default SSH port (22) to a non-standard port can help reduce the number of automated attacks targeting your device.
Free SSH Clients for Raspberry Pi
There are several free SSH clients available that are compatible with Raspberry Pi. Some popular options include:
1. PuTTY
PuTTY is a widely used SSH client for Windows users. It is lightweight, easy to use, and supports a variety of protocols, including SSH.
2. OpenSSH
OpenSSH is a free and open-source SSH client available for Linux and macOS. It is pre-installed on most Unix-based systems and offers a wide range of customization options.
3. MobaXterm
MobaXterm is an enhanced SSH client for Windows that includes additional features such as file transfer and remote desktop capabilities.
IoT Security Best Practices
Securing your IoT devices is crucial to protecting your network and data. Below are some best practices to follow:
- Regularly update your software and firmware to patch known vulnerabilities.
- Use firewalls and intrusion detection systems to monitor and block unauthorized access attempts.
- Limit access to your devices to trusted users only.
- Implement encryption for all data transmitted between devices.
Troubleshooting SSH Connections
Even with proper setup, SSH connections can sometimes fail. Below are some common issues and their solutions:
Connection Refused
This error typically occurs when SSH is not enabled on the server or the device is not connected to the network. Ensure that SSH is enabled and verify your network settings.
Permission Denied
If you receive a "permission denied" error, it may be due to incorrect credentials or disabled password authentication. Double-check your username and password, and ensure that password-based authentication is enabled.
SSH Alternatives for IoT
While SSH is a popular choice for IoT remote access, there are other protocols and tools that can be used depending on your specific needs:
1. MQTT
MQTT (Message Queuing Telemetry Transport) is a lightweight messaging protocol designed for IoT applications. It is ideal for low-bandwidth, high-latency networks.
2. VNC
VNC (Virtual Network Computing) allows you to remotely access the graphical interface of your Raspberry Pi. While not as secure as SSH, VNC can be useful for tasks that require a graphical environment.
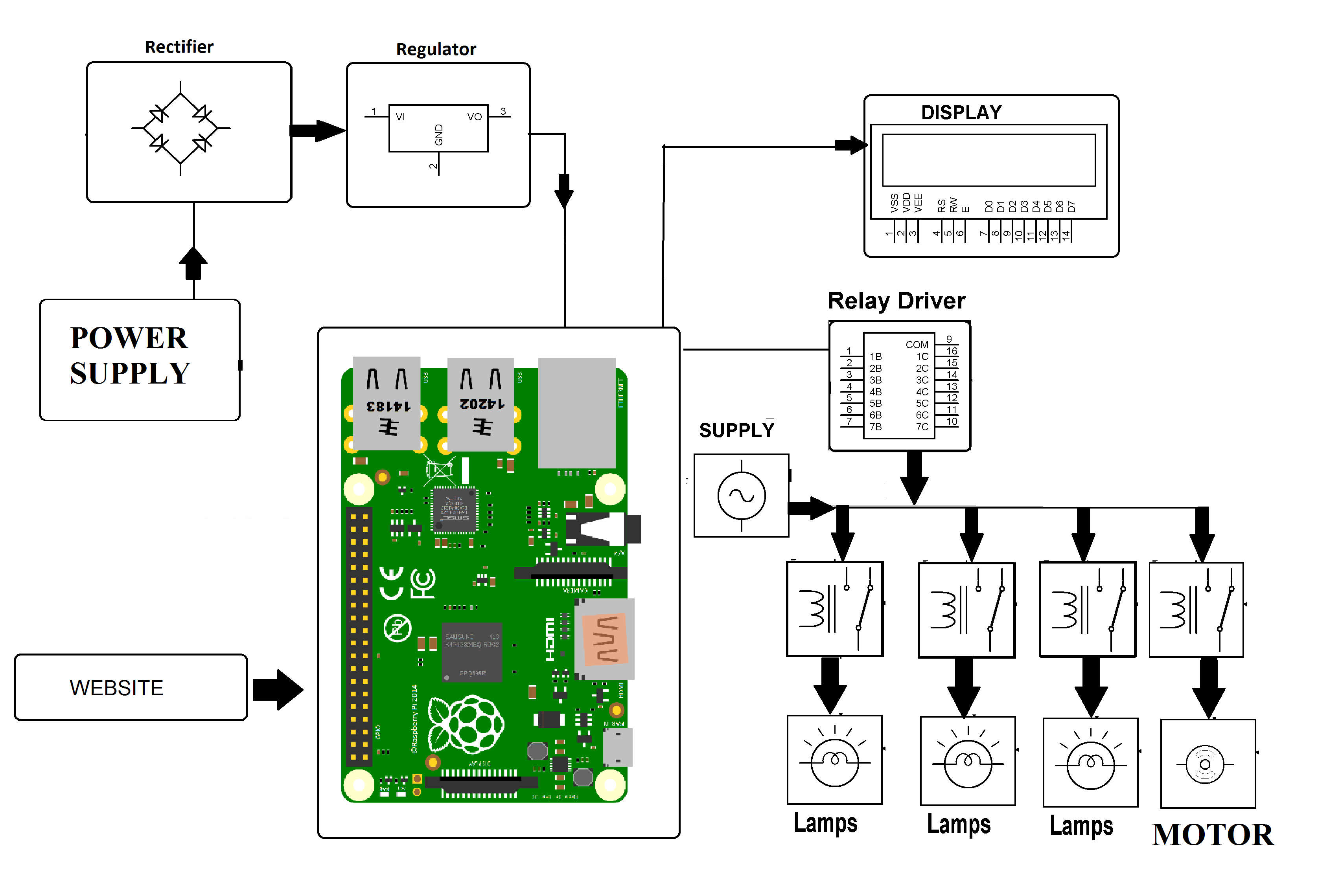
Real-World IoT SSH Applications
SSH remote IoT Raspberry Pi has been used in a variety of real-world applications, including:
- Home automation systems
- Smart agriculture solutions
- Remote weather monitoring stations
- Industrial IoT deployments
Conclusion and Next Steps
SSH remote IoT Raspberry Pi offers a secure and efficient way to manage IoT devices remotely. By following the steps outlined in this guide, you can set up and secure your SSH connections, ensuring that your projects remain protected and functional.
For further reading, consider exploring advanced topics such as SSH tunneling, certificate-based authentication, and IoT security frameworks. Additionally, don't forget to regularly update your devices and stay informed about the latest developments in IoT technology.
Feel free to leave a comment or share this article if you found it helpful. For more guides and resources, visit our website and explore our extensive library of IoT and Raspberry Pi content.